Resources
INTELLIGENCE DIGEST
Phishing. Credential Theft. Exfiltration. Extortion. The Saga Continues.
Ransomware gangs thrive, even against big firms like Cisco
By Rodman Ramezanian - Enterprise Cloud Security Advisor
August 25, 2022 7 Minute Read
Hot on the heels of numerous high-profile breaches at the hands of cybercrime gangs, Cisco undoubtedly takes no pleasure in confirming a breach of its corporate network in a recent extortion attack from the Yanluowang ransomware group.
With industry reports confirming a successful compromise of a Cisco employee’s credentials as a trigger, the news serves as yet another stark reminder of how destructive remote access abuse can be.
In this instance, the initial abuse of Cisco VPN was aided by stolen corporate credentials from within the Cisco employee’s personal Google account.
Once authenticated (thanks to further social engineering and voice phishing techniques), the attackers acquired access into Cisco’s corporate networks, enrolled a number of devices for Multi-Factor Authentication, and ultimately exfiltrated data for purposes of ransom and extortion.
Yet again, much like the Tactics, Techniques, and Procedures (TTP) used by similar groups like Lapsus$ and UNC2447, we see authenticated remote access via VPN being a critical threat vector aiding the data theft. The Yanluowang group claims to have stolen approx. 2.8GB of data.
As stated by Cisco’s own security teams, the attacker then escalated privileges to administrator level, allowing them to maneuver inside the network and login successfully to multiple systems. Herein lies the critical risk of lateral movements facilitated by unrestrained VPN access.
Why do these breaches occur?
Hybrid workforces blurring lines between personal cloud apps and business apps present unique challenges and increased risks. Unfortunately, these aren’t the sorts of risks that can be mitigated with a few different point products either!
Social engineering and phishing techniques employed by cyber criminals are nothing new. However, the continuing trend of corporate employees being duped by convincing schemes cannot be discounted.
As hybrid workforces continue to grow, attackers increasingly set their sights on obtaining remote access credentials. Why? A vast majority of enterprises are yet to abandon their traditional VPN technologies that grant unfettered access to corporate environments once authenticated.
Once these attackers acquire the necessary remote access tools and credentials, they’ll typically then divert their efforts towards deceiving victims using social engineering tactics to bypass Multi-Factor Authentication checks that usually follow.
Traditional Virtual Private Network (VPN) introduces the risk of excessive data exposure, as any remote user with valid login keys can get complete access to the entire internal corporate network and all resources within.
Just as hybrid workers will typically agree when working remotely, you can bet the threat actors are well aware of how valuable remote access is!
In the context of this incident involving Cisco, it’s clear to see how harmful compromised remote access, lateral movements, and privilege misuse can be to even the largest technology firms.
What can be done?
Given the threat actor’s proven competence in using a wide range of tactics to obtain initial access, user education is a vital requirement for countering Multi-Factor Authentication bypass techniques.
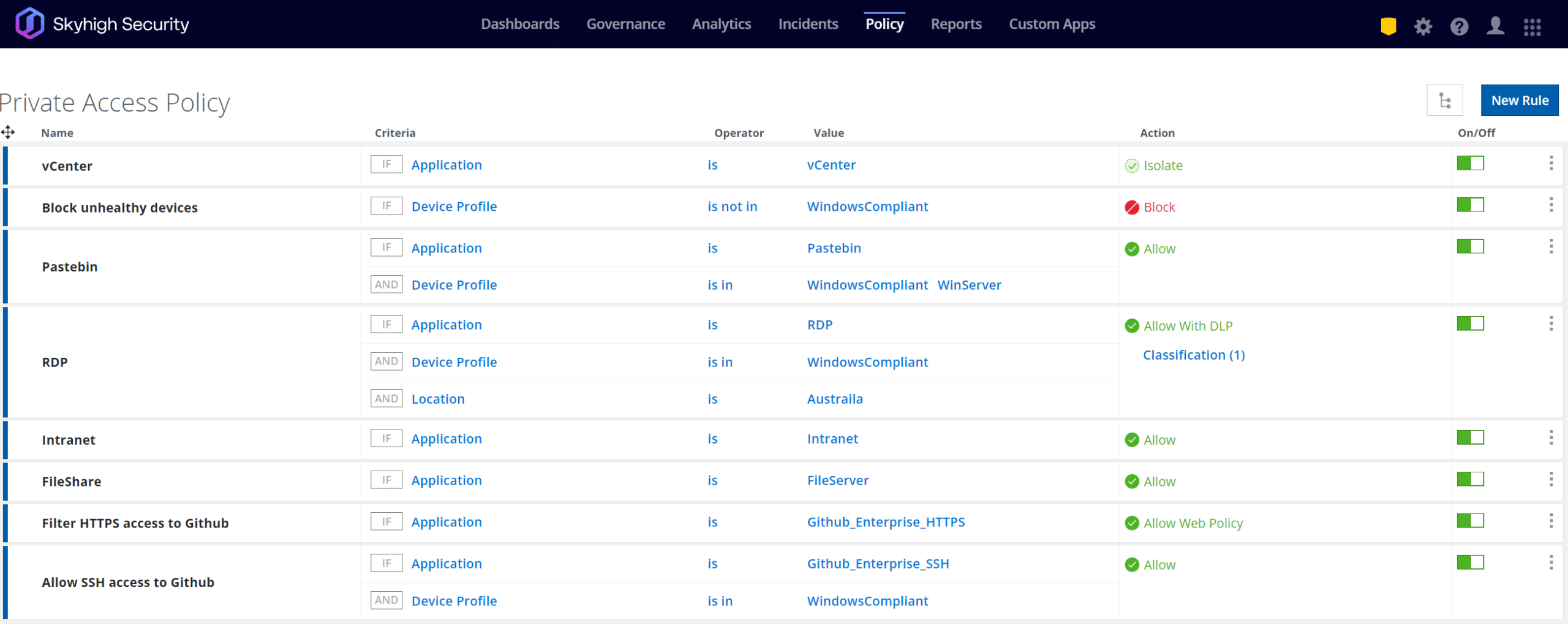
Considering the attacker’s misuse of administrative privileges, apply strong device checks by enforcing stricter controls to limit or block enrollment and access from unmanaged or unknown devices to corporate apps, networks, and services.
Network segmentation is another essential security control that organizations should utilize, as it provides enhanced protection for high-value assets and helps prevent lateral movements and data exfiltration attempts in situations where an adversary is able to gain initial access into the environment.
To help with adopting this guidance, organizations should avoid have one single, pipe in and out of their network. In a Zero Trust architecture, networks are instead segmented into smaller fragments where specific workloads are contained. Each fragment can have its own ingress and egress controls, posture checks, contextual access controls, data protections, and much more to minimize the “blast radius” of unauthorized access.
With a Zero Trust methodology, you increase the difficulty for unauthorized actors to propagate throughout your networks, thereby reducing the lateral movement of threats.
As data continues to be spread across our cloud infrastructures to enable productivity, ensure you not only enable content-aware collaboration controls between cloud apps, but also implement cloud Data Loss Prevention capabilities to avoid sacrificing security at the hands of a simple, compromised VPN session.
Use Skyhigh Security?
- Enable activity monitoring, data loss prevention, and threat protection for GitHub
- Monitor GitHub user activity in the Activity Monitoring page
- Block access to URLs based on reputation and domain categorization
- Manage and control access to private applications and services such as Remote Desktop Protocol (RDP)
- Implement content-aware collaboration controls for Box (as reported in Cisco incident) and many other cloud apps
- Analyze threats, anomalies, and suspicious behaviors relating to administrative privilege escalations
With over 11 years’ worth of extensive cybersecurity industry experience, Rodman Ramezanian is an Enterprise Cloud Security Advisor, responsible for Technical Advisory, Enablement, Solution Design and Architecture at Skyhigh Security. In this role, Rodman primarily focuses on Australian Federal Government, Defense, and Enterprise organizations.
Rodman specializes in the areas of Adversarial Threat Intelligence, Cyber Crime, Data Protection, and Cloud Security. He is an Australian Signals Directorate (ASD)-endorsed IRAP Assessor – currently holding CISSP, CCSP, CISA, CDPSE, Microsoft Azure, and MITRE ATT&CK CTI certifications.
Candidly, Rodman has a strong passion for articulating complex matters in simple terms, helping the average person and new security professionals understand the what, why, and how of cybersecurity.
Attack Highlights
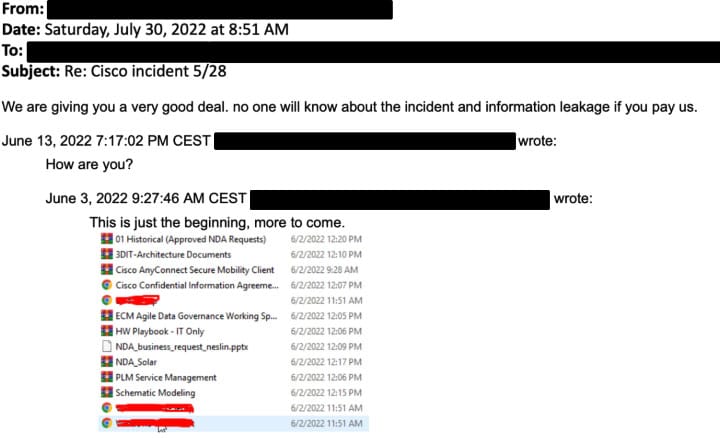
- Yanluowang ransomware group published a list of supposedly exfiltrated files, as spotted by security researchers
- Attackers begin to abuse native “AutoSave” and “Version Control” features that create cloud backups of older file versions (intended to help users recover older copies of edited files)
- Cisco employee’s credentials were compromised after an attacker gained control of a personal Google account where credentials saved in the victim’s browser were being synchronized
- Attacker conducted voice phishing attacks under the guise of various trusted organizations, attempting to convince the victim to accept Multi-Factor Authentication (MFA) push notifications initiated by the attacker
- Threat actor used a variety of techniques to escalate access and gain persistent access to network, as well as removing traces of intrusion
- Attacker dropped a variety of tools, including remote access tools like LogMeIn and TeamViewer, offensive security tools such as Cobalt Strike, PowerSploit, Mimikatz, and Impacket, and added their own backdoor accounts and persistence mechanisms
- Exfiltrated contents of a Box folder relating to compromised employee’s account and employee authentication data from Active Directory
- Malware payloads dropped by attacker onto compromised systems, including backdoor software designed to communicate with a command-and-control server









