Resources
INTELLIGENCE DIGEST
Learnings from Lapsus$ — the Advanced Persistent Teenagers?
Protecting against an extortion gang with a significant list of victims
By Rodman Ramezanian - Enterprise Cloud Security Advisor
June 9, 2022 7 Minute Read
The new hot name in ransomware attacks is Lapsus$. If you haven’t heard of them before, you’ve probably heard of some of the companies they attacked, including Nvidia, Samsung, Okta, and Microsoft – just to name a few. For the uninformed, Lapsus$ is a hacking group that focuses on data theft and extortion. The group mainly targets corporations, and has racked up quite a disconcerting array of noteworthy global casualties.
Often, LAPSUS$ abused the human weaknesses inside companies, such as their IT or customer support. In other cases, they purchased already hacked login tokens from dark-web marketplaces. Typically, some cybersecurity professionals may see these as low-level threats. The reality is that sophistication is not the only metric that makes a hacker more menacing; it’s also their audacity.

From employing social engineering tactics and SIM card swapping, to crafty phishing attacks and overt luring of internal employees, the Lapsus$ operators capitalise on offered resources to gain footholds into corporate network via popular means of VPN and Virtual Desktop Infrastructure (VDI).
This vividly highlights the fact that if humans work for you, you are vulnerable to social engineering. No one should be treated as incorruptible. The immediate implication for cloud resources is that you should reduce the access permissions people have to the very minimum they actually require in order to perform their job. As the cloud usually stores very sensitive resources, providing anyone who might be breached (virtually everyone!) with excessive permissions can cause unwarranted exposure to the crown jewels of the organization.
How did these breaches occur?
Predominantly using large-scale social engineering and manipulation techniques, the Lapsus$ group have accumulated an imposing list of victims globally. Interestingly, the incidents share a common approach; they all involved use of valid credentials, ultimately abusing whatever permissions had been granted to that identity. These attacks are a glaring reminder that authentication (who are you?) and authorization (what can you do?) are critical to security posture. The principles of least privilege and zero trust have never been more applicable.
What can be done?
Despite your best efforts for authentication and authorization, a breach can still happen at the hands of motivated insiders.
It begs the question, “How do you determine if a trusted, authorized entity’s actions are malicious?” Permission sets have a nasty habit of creeping and growing over time.

As part of a Zero Trust Network Access (ZTNA) approach, organizations are encouraged to segment their networks, posture assess their requesting devices, and contextually provision access to apps and resources (using DLP and Remote Browser Isolation capabilities).
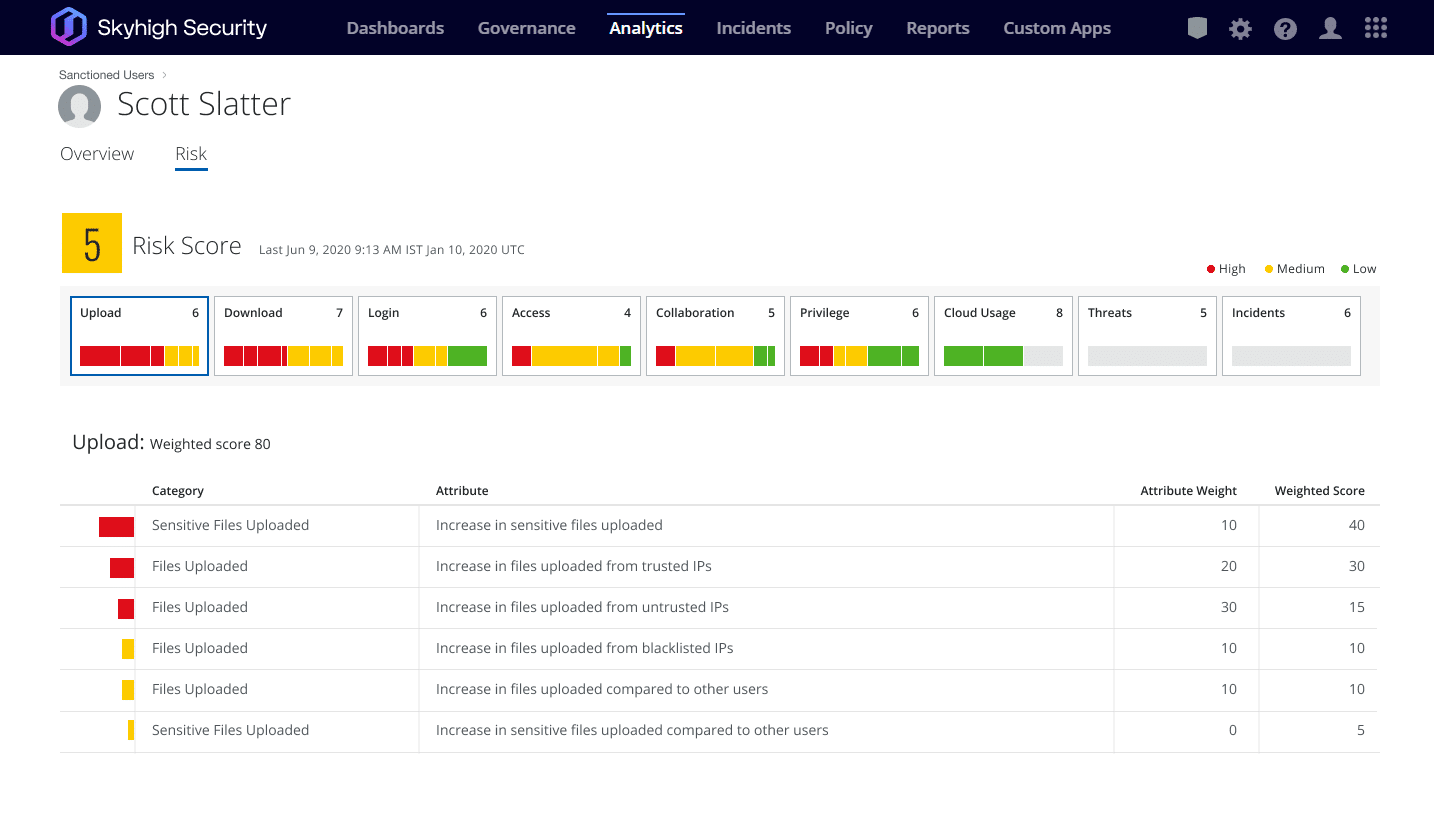
In the ill-fated case of an insider threat, Anomaly-based detections and Behavioral analysis capabilities can help spot and mitigate abnormal and potentially dangerous behaviors by building a baseline of “normal activity” for that specific context, to ultimately highlight any anomalies or deviations for swift action to be taken.
But, of course, security is more than just a collection of technical controls. Security practitioners must review the permissions, processes and procedures used by their stakeholders and trusted entities – both internal and third party. The aforementioned attacks have prompted the security world to take heed of these fundamentals.
Use Skyhigh Security?
- Leverage configuration audits to discover and monitor services exposed to unrestricted access
- Assess the posture of connecting devices using a variety of granular attributes
- Segment your infrastructure by dynamically controlling access to private apps and resources
- Protect your private apps and resources from being exposed to the internet
- Block unmanaged devices, enforce Multi-Factor Authentication and many other contextual access policies to help stop the successful reuse of stolen cloud application credentials
- Evaluate user activities beyond initial logins to include user movements, behaviours, access to corporate services, locations, and many other potential anomalies
With over 11 years’ worth of extensive cybersecurity industry experience, Rodman Ramezanian is an Enterprise Cloud Security Advisor, responsible for Technical Advisory, Enablement, Solution Design and Architecture at Skyhigh Security. In this role, Rodman primarily focuses on Australian Federal Government, Defense, and Enterprise organizations.
Rodman specializes in the areas of Adversarial Threat Intelligence, Cyber Crime, Data Protection, and Cloud Security. He is an Australian Signals Directorate (ASD)-endorsed IRAP Assessor – currently holding CISSP, CCSP, CISA, CDPSE, Microsoft Azure, and MITRE ATT&CK CTI certifications.
Candidly, Rodman has a strong passion for articulating complex matters in simple terms, helping the average person and new security professionals understand the what, why, and how of cybersecurity.
Attack Highlights
- Lapsus$ attacks Brazil’s Ministry of Health, demanding a ransom to avoid 50 TB of data leakage.
- String of attacks on Portuguese media firm Impresa, and Latin American telecom Claro.
- Vodafone source code stolen from their GitHub stores; Lapsus$ gloats via Telegram.
- Nvidia breached, losing almost one TB of exclusive code-signing certs and firmware.
- Third party customer support engineer working for Okta has account compromised, leading to 366 customers’ data stolen.
- Almost 200 GB of Samsung device source code and algorithms leaked via torrent file shared across Telegram.
- Gaming giant Ubisoft attacked, causing disruptions to services.
- Microsoft’s Bing, Cortana and other services breached, with partial source code shared by Lapsus$ via Telegram.









