What Is DSPM and Why Modern Enterprises Need It?
- DSPM gives enterprises continuous visibility into where sensitive data lives, how it's classified, and who can access it.
- DSPM is most effective as a data-centric layer that complements DLP, CASB, SSPM, and broader SSE strategies.
- Cloud, SaaS, and AI workflows have made continuous data discovery and risk prioritization essential.
- Strong DSPM programs focus on turning data context into prioritized, actionable remediation.
- Accurate data inventory and classification strengthen compliance, governance, and AI risk management.
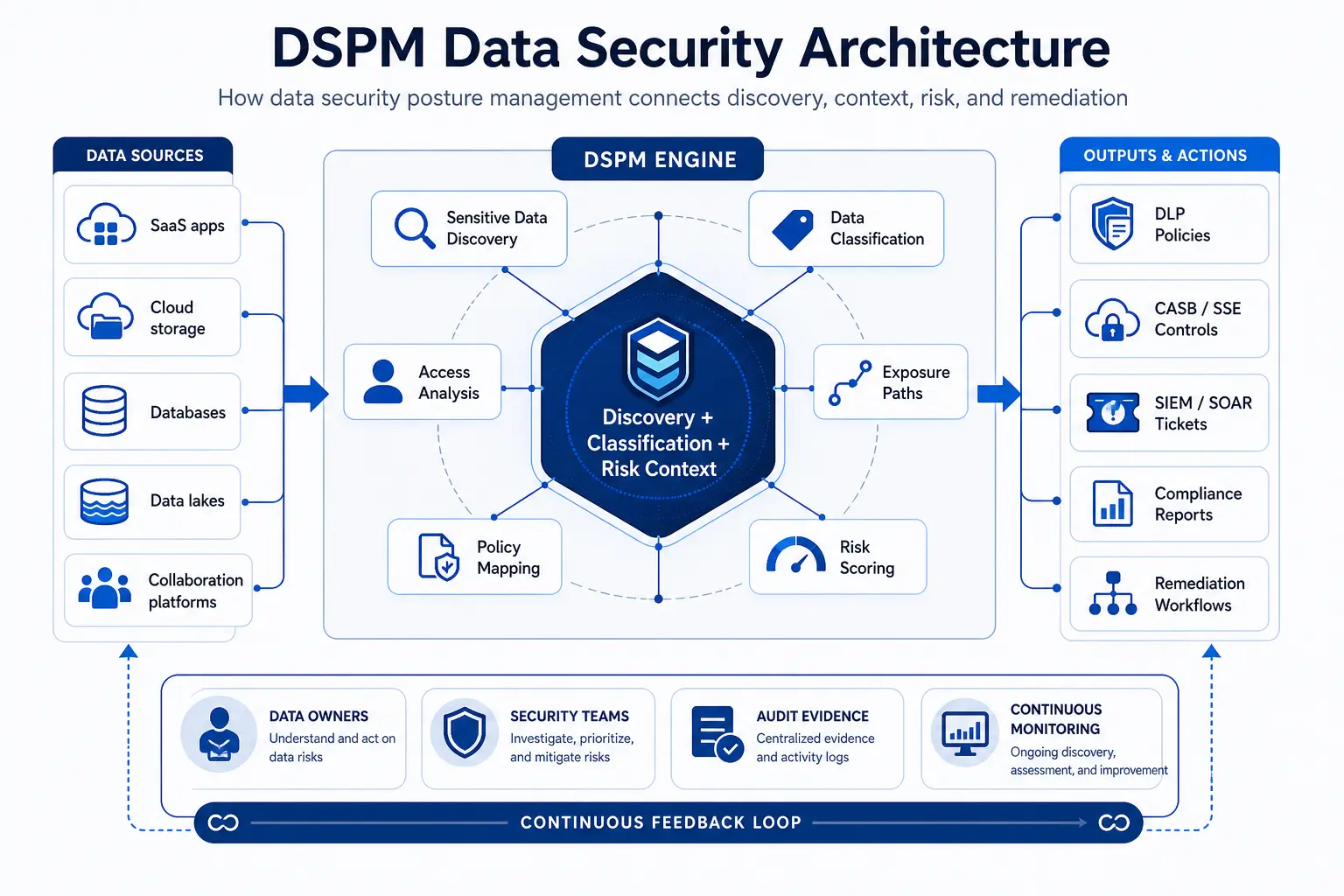
Data security posture management is the continuous process of finding sensitive data, classifying it, understanding its exposure, and monitoring data risk across cloud, SaaS, and hybrid environments.
As organizations expand across cloud, SaaS, analytics, and AI-enabled workflows, sensitive data tends to spread faster than traditional governance processes can keep up. That is why data security posture management has become a core part of modern security strategy: it helps teams discover sensitive data, classify it consistently, assess exposure, and prioritize remediation before risk becomes an incident.
Unlike a point-in-time scan, data security posture management is designed for continuous visibility. It helps security, privacy, compliance, and cloud teams understand what sensitive data exists, where it lives, who can access it, and which issues create the greatest risk.
This article explains what DSPM is, how it works, why it matters now, and how it compares with related controls such as DLP, CASB, and SSPM. For related cloud security concepts, see our Academy resources on Cloud Security Posture Management, Data Loss Prevention (DLP), SaaS Security Posture Management (SSPM), and Cloud Access Security Broker (CASB).
Within a broader Security Service Edge strategy, DSPM plays an important role by bringing data context to cloud and SaaS security decisions. That is especially relevant for enterprises looking to align data protection with a modern, unified approach to security. Skyhigh Security was recognized as a Niche Player in the 2025 Gartner Magic Quadrant for Security Service Edge and scored highest in the Data Security use case in the 2025 Gartner Critical Capabilities for SSE, reinforcing the importance of data-centric visibility as a practical foundation for enterprise risk reduction.
What is data security posture management?
Data security posture management is the continuous practice of discovering sensitive data, classifying it, understanding exposure and access context, and monitoring risk across modern environments.
Data security posture management is a data-centric security practice focused on discovering sensitive data, classifying it, understanding its exposure, and prioritizing remediation. In practical terms, it gives teams a reliable way to answer five questions:
- What sensitive data do we have?
- Where does it reside?
- How sensitive is it?
- Who can access it or expose it?
- Which posture issues create the most risk?
That makes DSPM a visibility and prioritization layer rather than just a scanner or a reporting tool. It helps teams move from inventory to context, and from context to action.
Why data security posture management matters now
DSPM matters because sensitive data is now distributed across cloud, SaaS, collaboration, analytics, backup, and AI-connected environments, making visibility and prioritization harder than before.
Cloud adoption increased the number of places data can live. SaaS adoption increased the number of people and apps that can touch it. AI adoption increased the urgency of knowing what data may be entering new tools, prompts, retrieval systems, and automated workflows. Together, these shifts make data security posture management more important for enterprises that need to reduce exposure without slowing business use cases.
Industry breach and threat reporting reinforces the need for stronger data visibility. Verizon’s 2026 Data Breach Investigations Report found the human element present in 62% of breaches, while IBM’s Cost of a Data Breach Report 2025 reported a global average breach cost of USD 4.44 million. In parallel, threat reporting continues to show that AI-related workflows and data handling are becoming a growing concern for security teams.
For organizations operating across cloud and SaaS, data security posture management helps bridge the gap between where sensitive data exists and where protective action should happen.
How DSPM works in practice
A mature DSPM program typically discovers data, classifies it, maps exposure, prioritizes the highest-risk issues, and helps teams remediate misconfigurations or access problems.
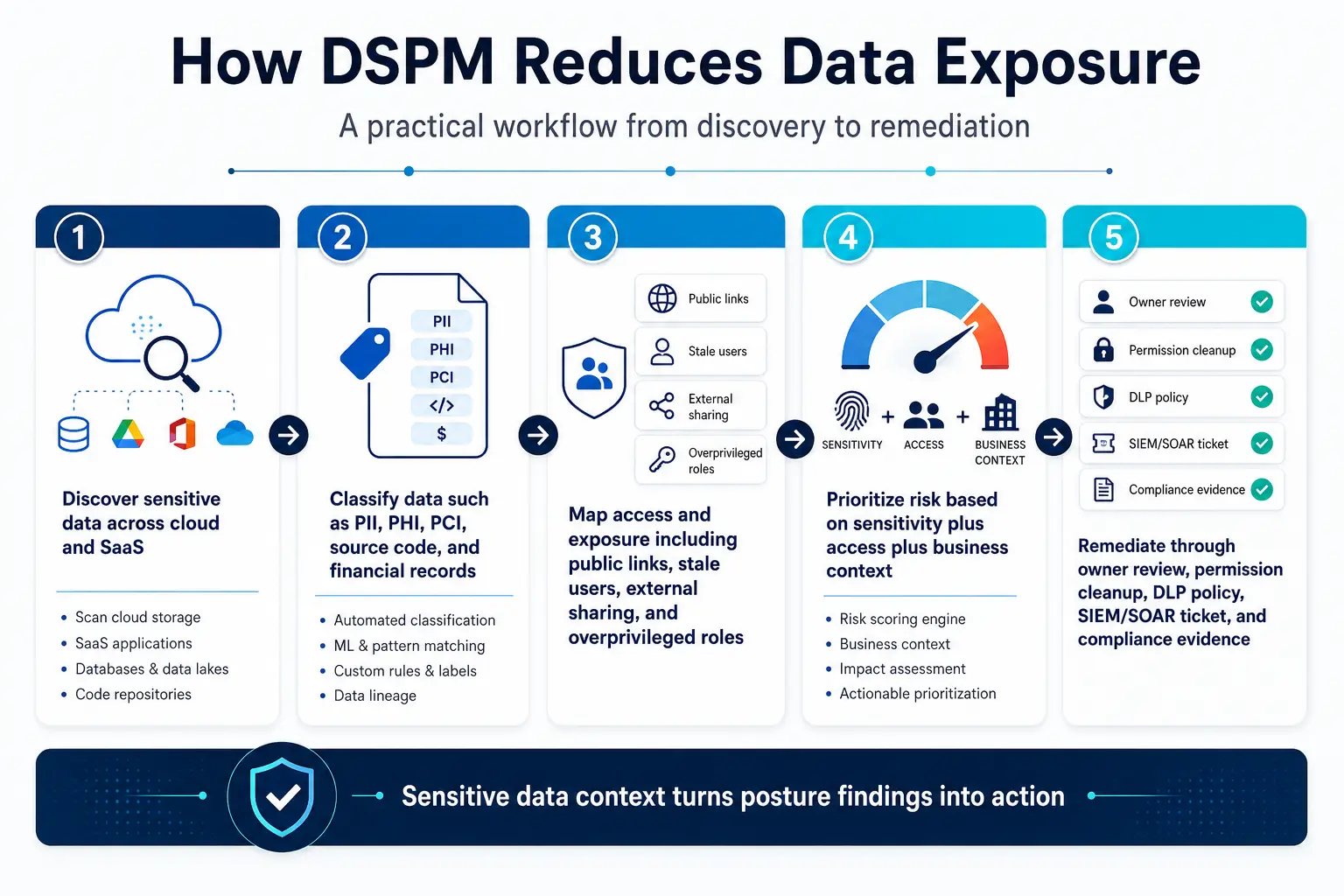
A practical data security posture management workflow usually includes the following steps:
1) Discover sensitive data
The first step is identifying where sensitive data resides across cloud storage, databases, file repositories, SaaS apps, backups, and other distributed systems. Without discovery, teams cannot understand the true scope of exposure.
2) Classify the data
Once data is found, it must be classified by type, sensitivity, ownership, and business context. Classification is foundational because downstream controls depend on whether the system knows what it is protecting.
3) Assess exposure and access
DSPM evaluates who can reach the data, whether permissions are excessive, whether sharing is too broad, and whether configurations create avoidable exposure. This is where posture management becomes actionable.
4) Prioritize the most important risks
Not every finding deserves the same response. Good DSPM tools help teams focus on the highest-risk combinations of sensitivity, exposure, and access.
5) Support remediation
The best programs connect findings to remediation workflows, so teams can reduce risk instead of simply cataloging it.
How DSPM fits with DLP, CASB, and SSPM
DSPM complements Data Loss and Prevention (DLP), Cloud Access Security Broker (CASB), and SaaS Security Posture Management (SSPM), by identifying and contextualizing sensitive data, while those controls focus on enforcement, cloud app access, or SaaS configuration risk.
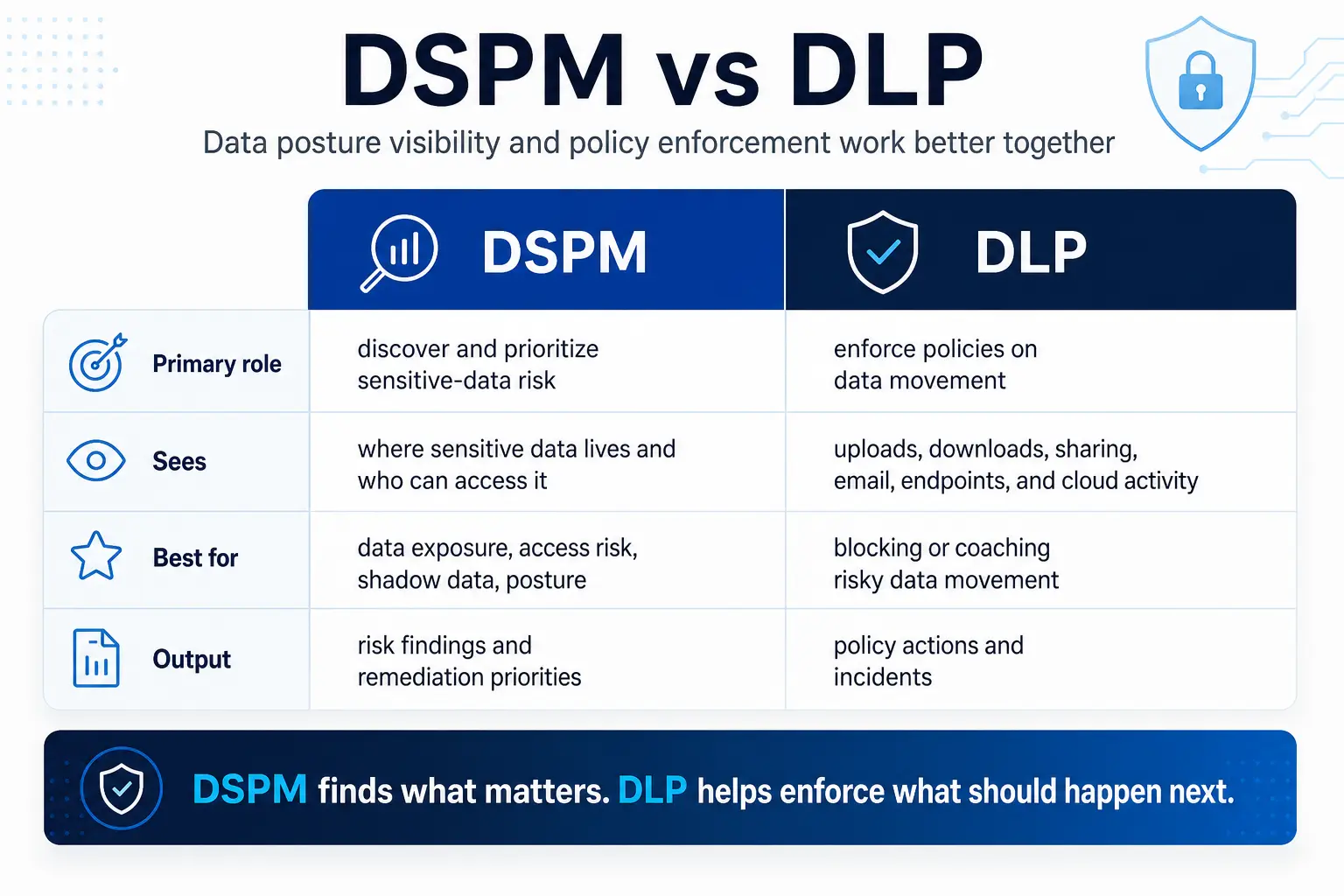
Data security posture management does not replace other security controls. It fills a different gap. DLP primarily enforces policies on how data is used, moved, or shared. DSPM focuses on finding the data first, understanding its sensitivity and exposure, and determining where enforcement matters most.
CASB and SSPM address adjacent problems around cloud app control and SaaS configuration security. DSPM complements them by adding a data-centric view of what sensitive information is actually at risk.
In enterprise architectures, these controls are strongest when they work together. DSPM provides the data context, while policy enforcement and access controls help organizations act on that context with precision.
What good DSPM should deliver
A strong DSPM solution should improve visibility, classification quality, risk prioritization, and the ability to act on findings in context.
When evaluating data security posture management, focus on whether the solution helps teams make better decisions rather than just produce more findings. A strong platform should support:
- Coverage across cloud and SaaS environments
- Classification quality and consistency
- Context on exposure, permissions, and sharing
- Prioritization that highlights the most urgent issues
- Remediation support and workflow integration
- Fit with broader data security and governance programs
That evaluation approach also helps security leaders decide whether DSPM is being used as a standalone scanner or as part of a broader operational process.
DSPM, compliance, and AI risk
DSPM supports compliance and AI governance by making sensitive data inventory, classification, and exposure continuously visible.
Compliance programs depend on knowing where sensitive data is stored and how it is accessed. Data security posture management helps because it makes inventory, classification, and exposure visible across distributed environments. That visibility supports privacy, governance, and audit readiness, especially where data is duplicated or shared across multiple systems.
NIST’s AI Risk Management Framework and the NIST AI 600-1 Generative AI Profile reinforce this theme through Govern, Map, Measure, and Manage functions that help organizations address risks related to data used in AI systems and workflows. NIST’s 2026 concept note for a trustworthy AI profile for critical infrastructure further underscores that AI governance expectations continue to evolve. In parallel, enterprise data classification guidance continues to emphasize that classification quality matters because it informs policy and control selection.
For organizations adopting AI, DSPM can help answer a critical question: what sensitive data is available to new workflows, tools, and retrieval systems before exposure becomes difficult to reverse?
This is also where a data-centric security model becomes especially valuable. Rather than treating every workflow the same, organizations can apply controls based on the sensitivity, location, and exposure of the data itself.
How to evaluate a DSPM program or vendor
Evaluate DSPM by checking data coverage, classification quality, exposure analysis, prioritization, remediation support, and how well it integrates with your security stack.
Before you adopt data security posture management, assess the following:
- Coverage: Does it inspect the cloud and SaaS environments you actually use?
- Classification: Can it identify sensitive data accurately and consistently?
- Context: Does it explain exposure, sharing, permissions, and posture issues?
- Prioritization: Can it separate urgent risks from noise?
- Remediation: Does it connect findings to practical action?
- Integration: Can it work with existing DLP, CASB, SSPM, SIEM, and governance processes?
For enterprise buyers, it is also worth assessing whether a DSPM capability fits within a broader, unified security architecture. Solutions that align data visibility with enforcement and access controls can help reduce operational complexity while improving consistency across cloud and SaaS environments.