Resources
Six Key Takeaways from RSA Conference 2023
By Thyaga Vasudevan - VP of Products, Skyhigh Security
May 17, 2023 3 Minute Read

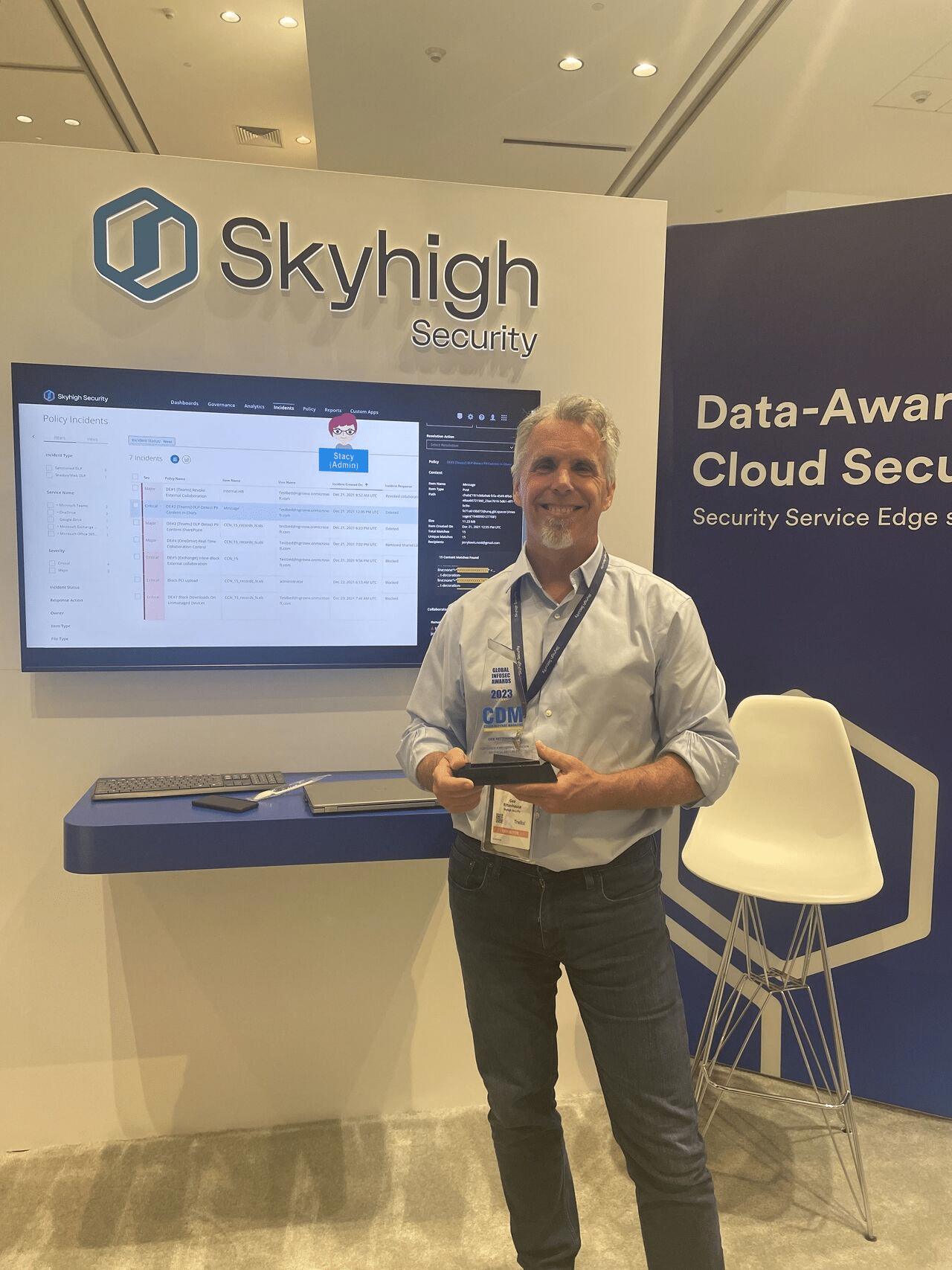
Skyhigh Security had a significant presence at RSA Conference 2023, which wrapped up recently in San Francisco, California. We showcased our differentiated Cloud Security product offerings in the Skyhigh Security booth, announced new product innovations, conducted theater sessions, customer meetings, press and analyst meetings, and held our highly anticipated Customer Advisory Board session. In addition, we took home two trophies from the coveted Global InfoSec Awards. The first for Most Innovative Cloud-Native Security. The second, for our fearless CEO, Gee Rittenhouse, whom received the Top Chief Executive Officer. I have to say, it was fantastic to meet up and connect with colleagues, customers and prospects in person.

After going through this whirlwind of meetings and discussions, and frequently shuttling between the Intercontinental Hotel and Moscone Center, I finally got the time to put together a few thoughts and trends that emerged for me at RSA – in no particular order:
- Artificial Intelligence and Machine Learning: AI and Machine Learning technologies, driven in part by the popularity of tools like ChatGPT are increasingly being used in cybersecurity to help identify and respond to threats in real-time. Experts at the RSA Conference emphasized the importance of incorporating these technologies into existing cybersecurity strategies. Also different companies are responding to the growth of AI tools within their own companies differently. We addressed this in this wonderful post.
- Remote Work is driving a lot of Cybersecurity use cases: With remote work becoming increasingly common, organizations face new challenges in securing their networks and data. The RSA Conference 2023 focused a lot on best practices for remote work cybersecurity, including secure remote access and network segmentation. The concept of zero trust, which assumes that all users, devices, and networks are potentially compromised, continued to gain popularity in the conference and with our customers as well. Every customer was planning on a ZTNA product solution either immediately or in the near future.
- Convergence of Data Protection and Threat Protection across the entire SSE security stack is a much-desired outcome – Many customers at the Customer Advisor Board (CAB) highlighted the value of a Unified DLP and Threat Protection solution across endpoint, Web, Cloud and Skyhigh Private Access, and clearly communicated to us how big a value that is for them.
- Cloud Security is no longer an afterthought – it is a front-and-center seat in board room discussions. In many customer meetings, it was clear that people already acknowledge the importance of protecting access and data on the cloud. We did less education for the customers for cloud security this year than before. Also, we were seeing the emergence of customers’ requirements to include the entire Security Service Edge (SSE) stack. They were either in the process of updating their requirements or were planning to get an SSE RFP out in the near future .
- Automation is key – While that was good to hear that cloud security was gaining traction, just like any other organization across the world, most security teams are struggling to find good talent in their organization. As such, they want to be able to automate as many workflows as possible. For example, incident remediation, notifications, and business workflows. Also, a guided advisor like the Cloud Security Advisor is something they would love in their environment.
- Cybersecurity Regulation and Compliance: With increasing regulatory requirements and compliance standards, customers at the RSA Conference discussed strategies for complying with regulations such as GDPR, CCPA, and HIPAA, and the role of Government in cybersecurity. With increased focus on cybersecurity by the Government, many of the different Govt bodies are partnering with Cloud security vendors – but of course, you need to have be either IL5 or FedRAMP certified to even consider doing business with these organizations.
We understand not everyone was able to make it to the event, so we’ve recorded our two booth demos: How to Gain Control of Your Cloud Security in a “Work from Anywhere” World and How to Protect Your Data: Unified Data Protection Across Endpoint, Network, and Cloud. Be sure to visit www.skyhighsecurity.com for more information.
Back to BlogsRelated Content

Securing the Fragmentation of the Modern Enterprise: The Data Hosting Conundrum
Trending Blogs
Skyhigh Security Renews IRAP Assessment at PROTECTED Level for 2026
Sarang Warudkar and Stuart Bayliss May 21, 2026
The Browser Security Gap Enterprises Can No Longer Ignore
Sarang Warudkar May 19, 2026
Securing the Fragmentation of the Modern Enterprise: The Data Hosting Conundrum
Ste Nadin May 14, 2026
Skyhigh Security Achieves SOC 2 Type II Compliance for the Complete SSE Cloud Platform
Sarang Warudkar and Stuart Bayliss April 30, 2026
Resilient Web Access Infrastructure: Business Imperative in a Cloud and Vibe-Code Obsessed World
Nick LeBrun April 23, 2026










