Skyhigh Cloud Access Security Broker
Secure Your Cloud Apps Without Compromising Your Security
Secure corporate data in cloud applications from exfiltration to unauthorized users or devices while keeping your employees productive
Securing the Future of Cloud Applications
Skyhigh AI stands as your ultimate defense, ensuring seamless and safe collaboration from any device, anywhere. Elevate your cybersecurity strategy and experience with the transformative power of our cutting-edge solutions.
Learn More
What makes us better than the rest
Skyhigh CASB provides unmatched data protection, device-based controls, and inline threat protection for all cloud applications using multi-mode cloud solution— all from a single platform.
Monitor and Regulate Access to Cloud Apps
Skyhigh CASB through its inline deployment modes (forward and reverse proxy) enables real-time control over user access to sanctioned and unsanctioned cloud services. No other CASB vendor has matched the comprehensive multi-mode coverage provided by Skyhigh Security. Read More
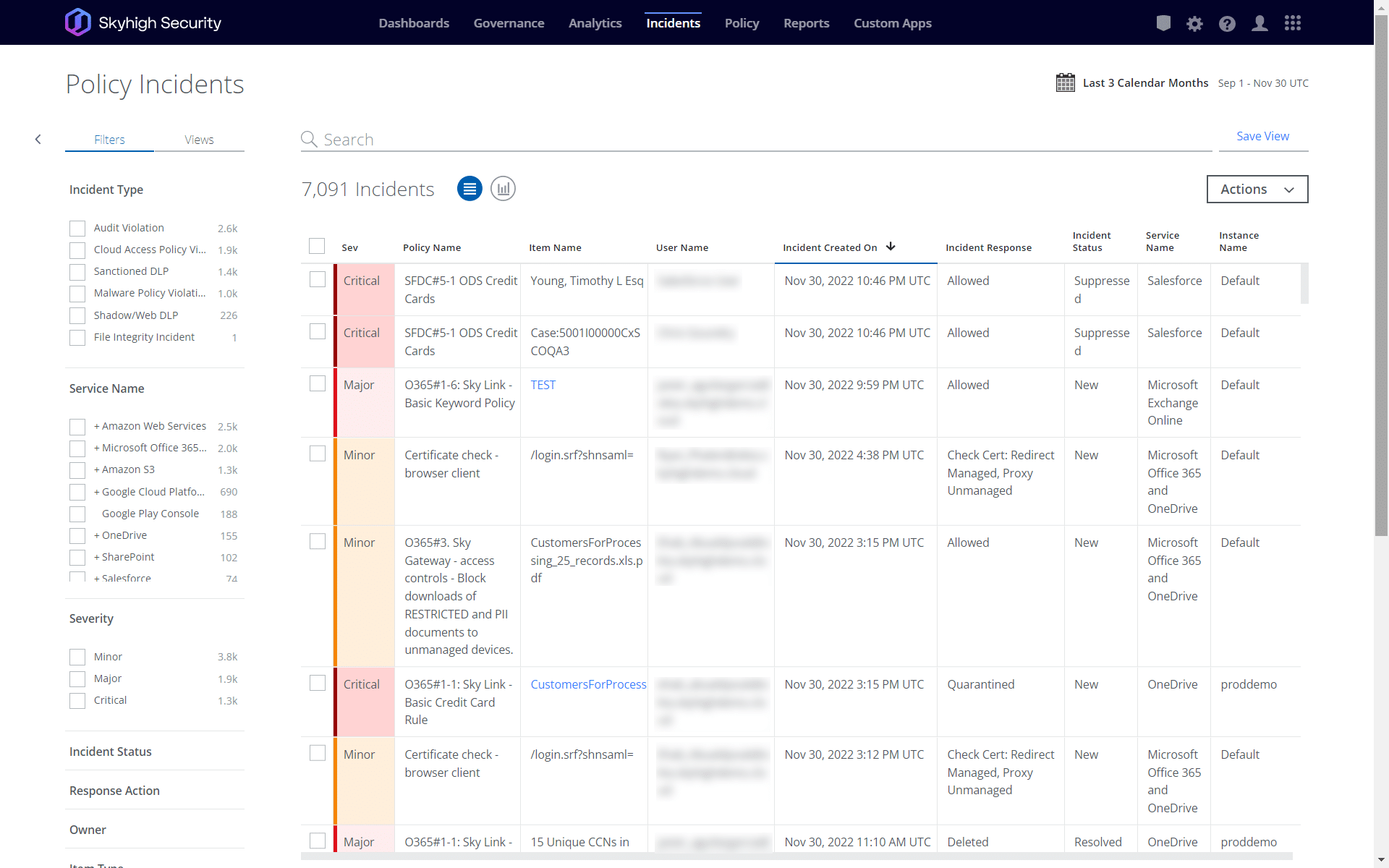
Control Over Data and Cloud Activity From Any Source
Gain control of your data across all cloud services and leverage the Skyhigh SSE framework to extend data protection capabilities to web, your network and endpoints through unified policy enforcement and incident management. Read More
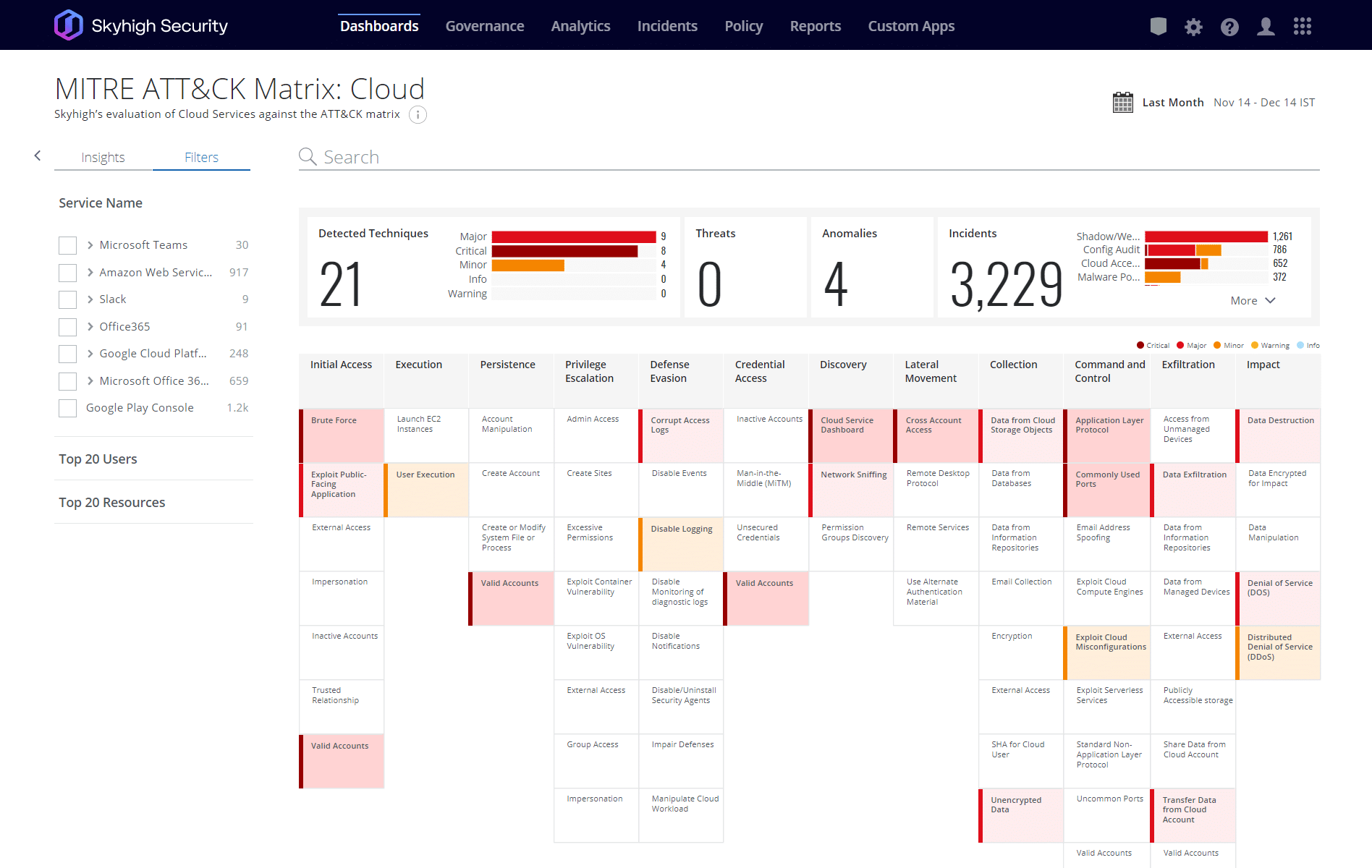
Protect Against Cloud Security Threats and Misconfigurations
Analyze billions of cloud events with machine learning to detect and mitigate threats occurring throughout your portfolio of cloud services. Reduce the risk of misconfiguration through continuous auditing and automated remediation of detected vulnerabilities. Skyhigh Security is the first CASB vendor to introduce MITRE ATT&CK mapping into the multi-cloud workflow. Read More
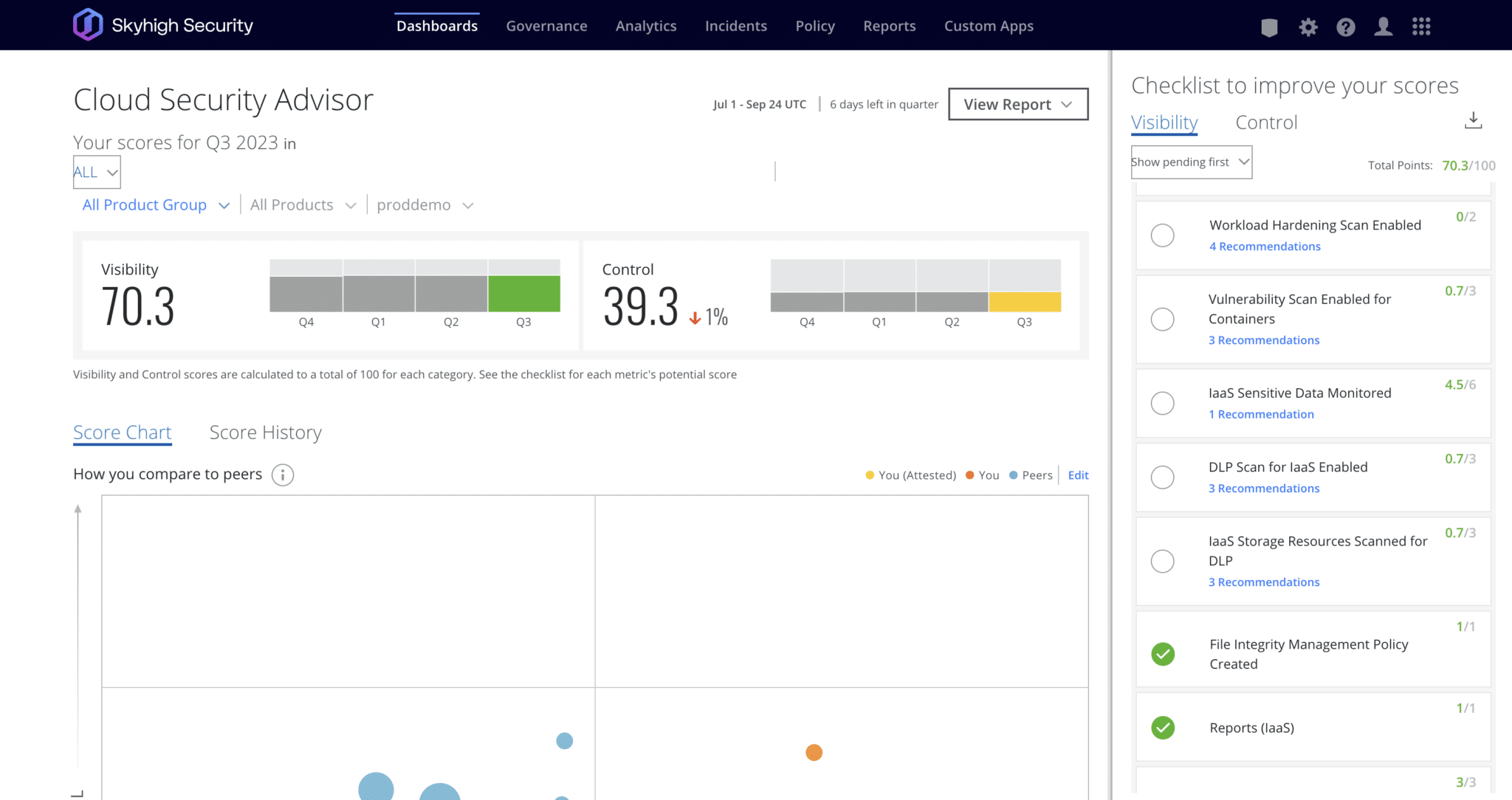
Gain Visibility into the Cloud Environment
Access a summary of the Shadow IT and Sanctioned cloud services configured in your organization. Measure and improve your cloud environment in comparison with your peers, review policy violation insights in your cloud environment, and implement recommendations to improve your security maturity. Cloud Security Advisor helps configure and fine-tune your Skyhigh CASB deployment. Read More

Skyhigh Secure Web Gateway (SWG) for Cloud has been granted FedRAMP High Authorization
With the Highest authorization of FedRAMP, Skyhigh SWG continues to meet customer demand as federal and public sectors embrace cloud-delivered security solutions.
The most comprehensive
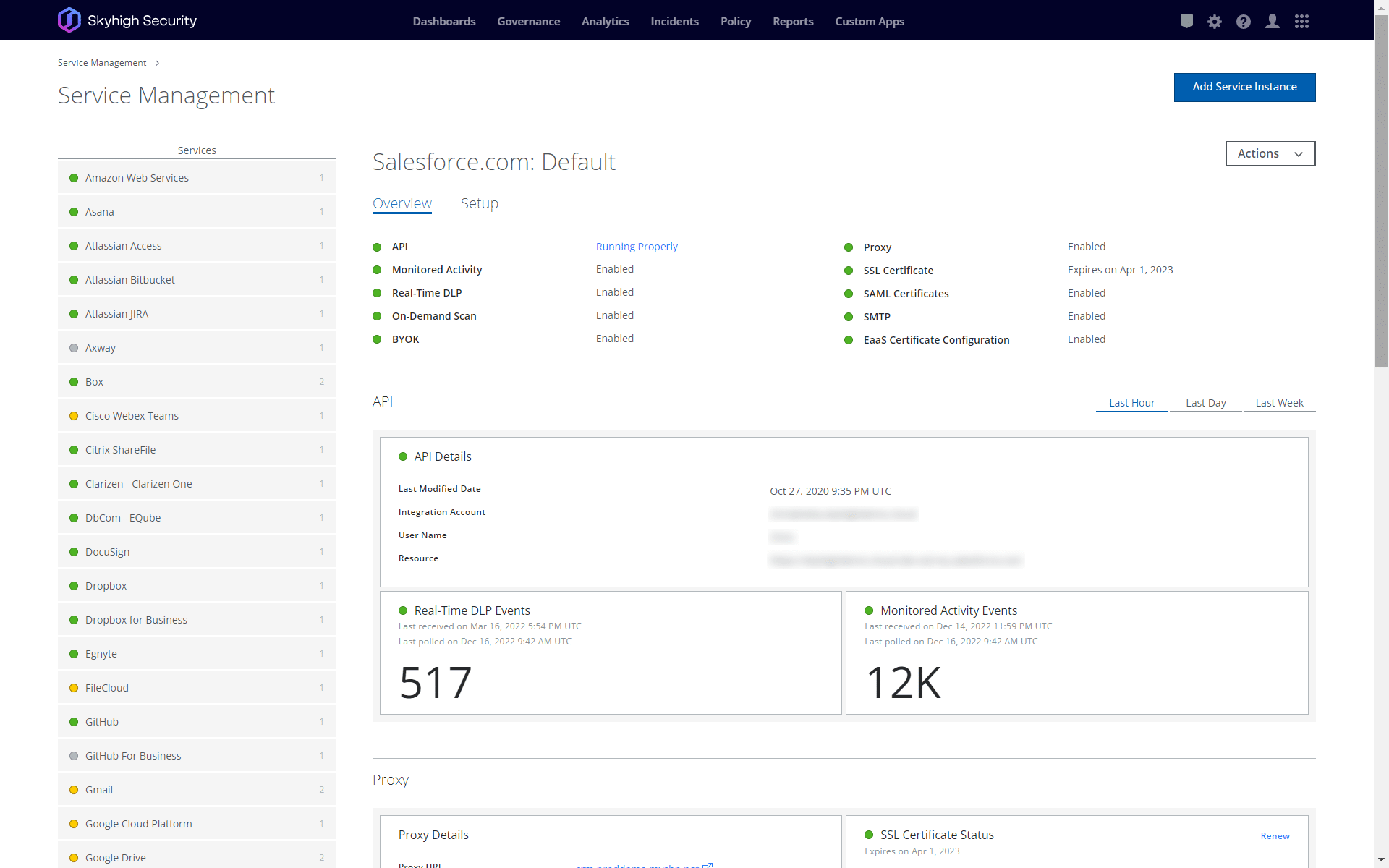
API integration in the industry
Support API integration for 40 apps































Skyhigh Security for ServiceNow provides the industry-leading Cloud Access Security Broker (CASB) solution to help organizations securely accelerate their business by providing total control over data and user activity in ServiceNow.
Read Data Sheet
Move your cloud transformation forward without sacrificing data or user security
Enables the secure adoption of company-approved cloud services, such as O365, Box, ServiceNow, and Salesforce, by providing activity monitoring, threat detection, and data protection through:
- Unified DLP
- EDM
- IDM
- OCR
- Collaboration Controls
- Device-based Controls
- Threat Protection/UEBA Malware Protection
- Tenant Restrictions
Go beyond traditional Firewall and Proxy Logs, offering visibility into cloud applications, that may or may not be supported by the IT Department, like GitHub, PDF, Evernote, LinkedIn, and Facebook, through:
- Unified DLP
- Cloud Registry
- User Risk Score
- Service Groups
- Activity Controls
- Activity Monitoring
- Unmatched Uploads
Key Metrics
Visibility of Assets Beyond On-premise Solutions
75+ attribute risk assessments
40,000+ cloud services
World’s largest and most accurate cloud service registry
40 API integration apps
Request a DemoProduct Features & Capabilities
What you can expect from Skyhigh CASB
Always know where your data is stored and discover sensitive data at rest within your cloud services. Quickly remediate any content that violates your company policies
Apply real-time controls to protect your data as user activity occurs, including granular content sharing and access controls
Gain access to the world’s largest and most accurate registry of cloud services based on a customizable 261-point risk assessment to support risk-aware cloud governance
Capture a comprehensive audit trail of all user and administrator activities to support post-incident investigations and forensics
Leverage machine learning to detect negligent and malicious behaviour including insider threat actor activity
Protect sensitive, structured data with peer-reviewed, function-preserving encryption schemes using enterprise-controlled keys
Cloud Security Use Cases
Skyhigh Cloud Access Security Broker enables organizations to embrace cloud technology while lowering their overall security risk and operating costs. Some of the most common use cases for CASB are:
- Understanding the risk of each cloud service
- Reporting on shadow IT usage
- Blocking access to risky cloud apps
- Gaining granular visibility and control of cloud app usage
Resources