
What is Zero Trust Network Access (ZTNA)?
Common ZTNA Use Cases
- Securing remote access to private applications
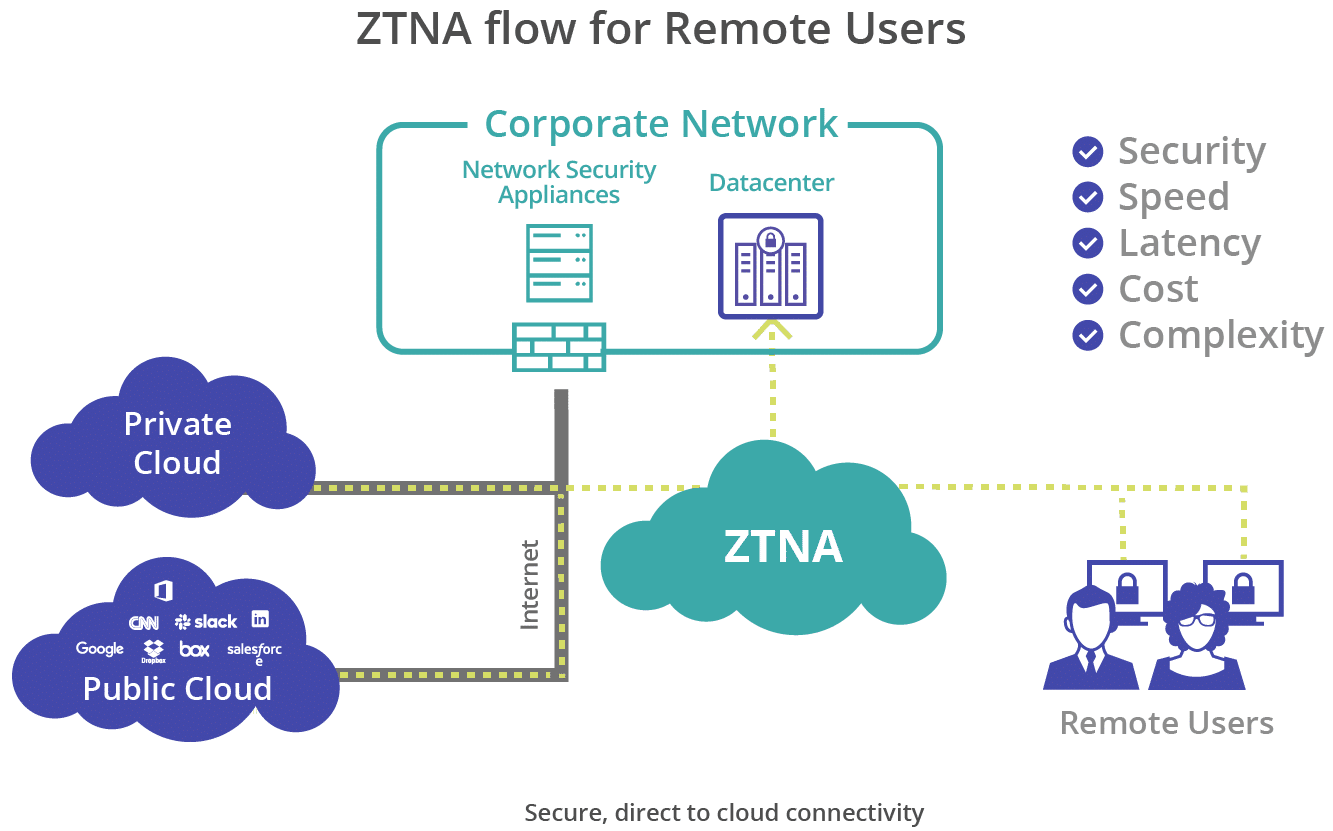
As organizations move their business-critical applications across multiple cloud environments for seamless collaboration, they are specifically challenged to monitor each connecting device to secure the application access and prevent data exfiltration. ZTNAs enable adaptive, context-aware access to private applications from any location and device. Access to applications is denied by default, unless explicitly allowed. The context for application access may include user identity, device type, user location, device security posture, etc. - Replacing VPN and MPLS connections
VPN architectures are slow and counter-productive in cloud-first deployments. Securing every remote user access through software and hardware-intensive VPNs can increase the capital expenditure and bandwidth costs. ZTNA provides fast, direct-to-cloud access to the corporate resources, reducing network complexity, cost, and latency, while significantly improving the performance to facilitate remote workforce deployments. - Limiting user access
The broad, perimeter-based security approach of traditional security solutions permit full network access to any user with valid login keys, over-exposing sensitive corporate resources to compromised accounts and insider threats. Hackers gaining access to the entire underlying network can move freely through the internal systems undetected. ZTNA implements least privileged controlled access, restricting user access to specific applications strictly on a “need to know” basis. All connections requests are verified before granting access to the internal resources.
Benefits of ZTNA
Micro-segmenting the networks
ZTNA allows organizations to create software-defined perimeters and divide the corporate network into multiple micro-segments, preventing lateral movement of threats and reducing the attack surface in case of a breach.
Making the applications invisible on internet
ZTNA creates a virtual darknet and prevents application discovery on public internet, securing organizations from internet-based data exposure, malware, and DDoS attacks.
Securing access to legacy applications
ZTNA can extend its benefits to legacy applications hosted in private data centers, facilitating secure connectivity, and offering the same level of security advantages as web applications.
Elevating the user experience
ZTNA enables secure, fast, uninterrupted, direct-to-cloud access to private applications, providing a consistent experience to remote users accessing both SaaS and private applications.
What’s the difference between VPN and ZTNA?
 Network-level access vs application-level access: VPNs permit full private network access to any user with valid login keys. ZTNA restricts user access to specific applications, limiting the data exposure and lateral movement of threats in case of any cyberattack.
Network-level access vs application-level access: VPNs permit full private network access to any user with valid login keys. ZTNA restricts user access to specific applications, limiting the data exposure and lateral movement of threats in case of any cyberattack.
Deep visibility into user activity: VPNs lack application-level controls and have no visibility to the user actions once he’s inside the private network. ZTNAs log every user action and provide deeper visibility and monitoring into the user behavior and risks to enforce informed, data-centric controls for securing sensitive content within applications. The logs can be fed to SIEM tools for real-time and centralized visibility into user activity and threats. ZTNAs can further be integrated with endpoint security solution to allow adaptive access based on continuous assessment of device security posture.
 Endpoint posture assessment: VPN connections don’t take into factor the risks posed by end-user devices. A compromised or malware infected device can easily connect to the server and gain access to internal resources. ZTNAs perform continuous assessment of connecting devices by validating their security posture and enable adaptive access to resources based on the device trust required at the time. The device connection is immediately terminated on detection of risks.
Endpoint posture assessment: VPN connections don’t take into factor the risks posed by end-user devices. A compromised or malware infected device can easily connect to the server and gain access to internal resources. ZTNAs perform continuous assessment of connecting devices by validating their security posture and enable adaptive access to resources based on the device trust required at the time. The device connection is immediately terminated on detection of risks.
User experience: VPN’s are not designed to handle the increasingly distributed workforce scenario. Backhauling every user connection through centralized VPN hubs creates bandwidth and performance issues, while leading to sub-par user experience. With ZTNA, users can establish direct-to-app connections, enabling fast and secure access to corporate resources hosted either in IaaS environments or private data centers, while facilitating agile and scalable cloud deployments.
Cost savings: ZTNA eliminates the need to procure the expensive VPN hardware and manage the complex infrastructure setup at each data center. Additionally, the remote users don’t need an additional, resource-intensive VPN client for establishing secure connection.
How does ZTNA work?
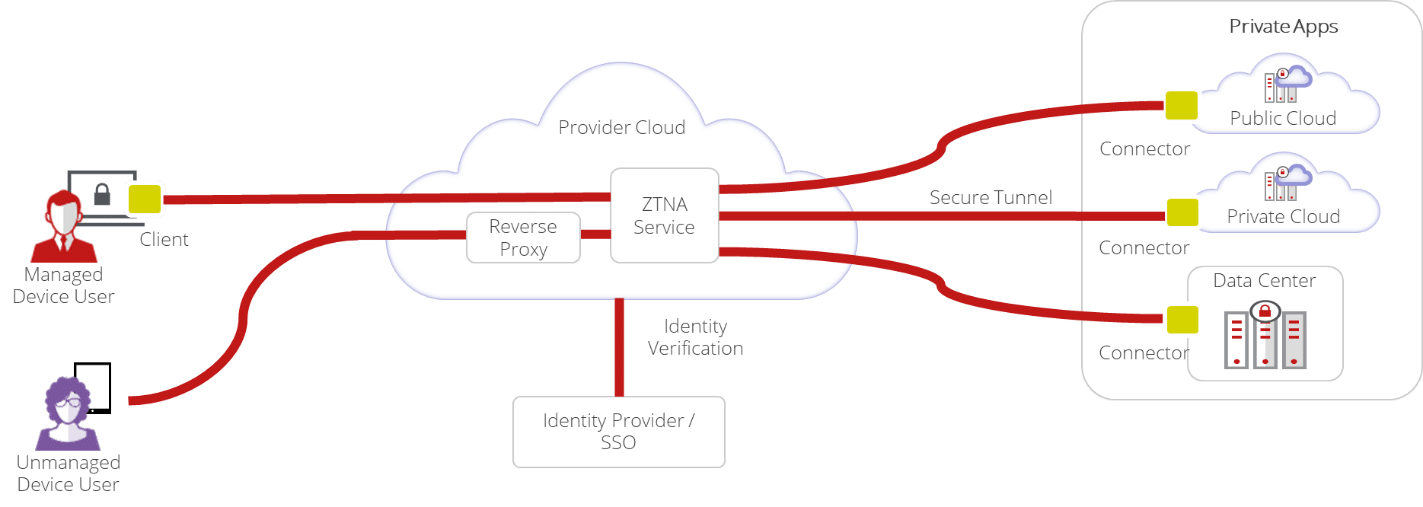
A connector software installed in the same customer network as the private application establishes an outbound connection to the service (or broker) hosted on the cloud through a secure, encrypted tunnel. The service is the egress point for private traffic into the customer network and is primarily responsible for:
- Verifying connecting users and authenticating their identity through an identity provider.
- Validating the security posture of the user devices.
- Provisioning access to specific applications through the secure tunnel.
Because of outbound, or “inside out”, connections to the ZTNA service, organizations don’t need to open any inbound firewall ports for application access, shielding them from direct exposure on the public internet, securing them from DDoS, malware, and other online attacks.
ZTNA can cater to both managed and unmanaged devices. Managed devices follow a client-based approach where a company owned client or agent is installed on the devices. The client is responsible for fetching the device information and sharing the details with the ZTNA service. Connection is established with applications on validation of user identity and device security posture.
Unmanaged devices follow a clientless or reverse-proxy based approach. The devices connect to the ZTNA service through browser-initiated sessions for authentication and application access. While this makes it an attractive prospect for third-party users, partners, and employees connecting through personal or BYO devices, clientless ZTNA deployments are limited to application protocols supported by the web browsers, such as RDP, SSH, VNC, and HTTP.
Introducing Skyhigh Private Access
Skyhigh Private Access is the industry’s first data-aware solution that enables granular “Zero Trust” access to private applications, from any location and device, and offers integrated data loss prevention (DLP) capabilities for securing data collaboration over ZTNA.








