The AI—Zero-Trust Nexus: How Defense CIOs Secure and Scale AI at Speed
Skyhigh Security | Reports
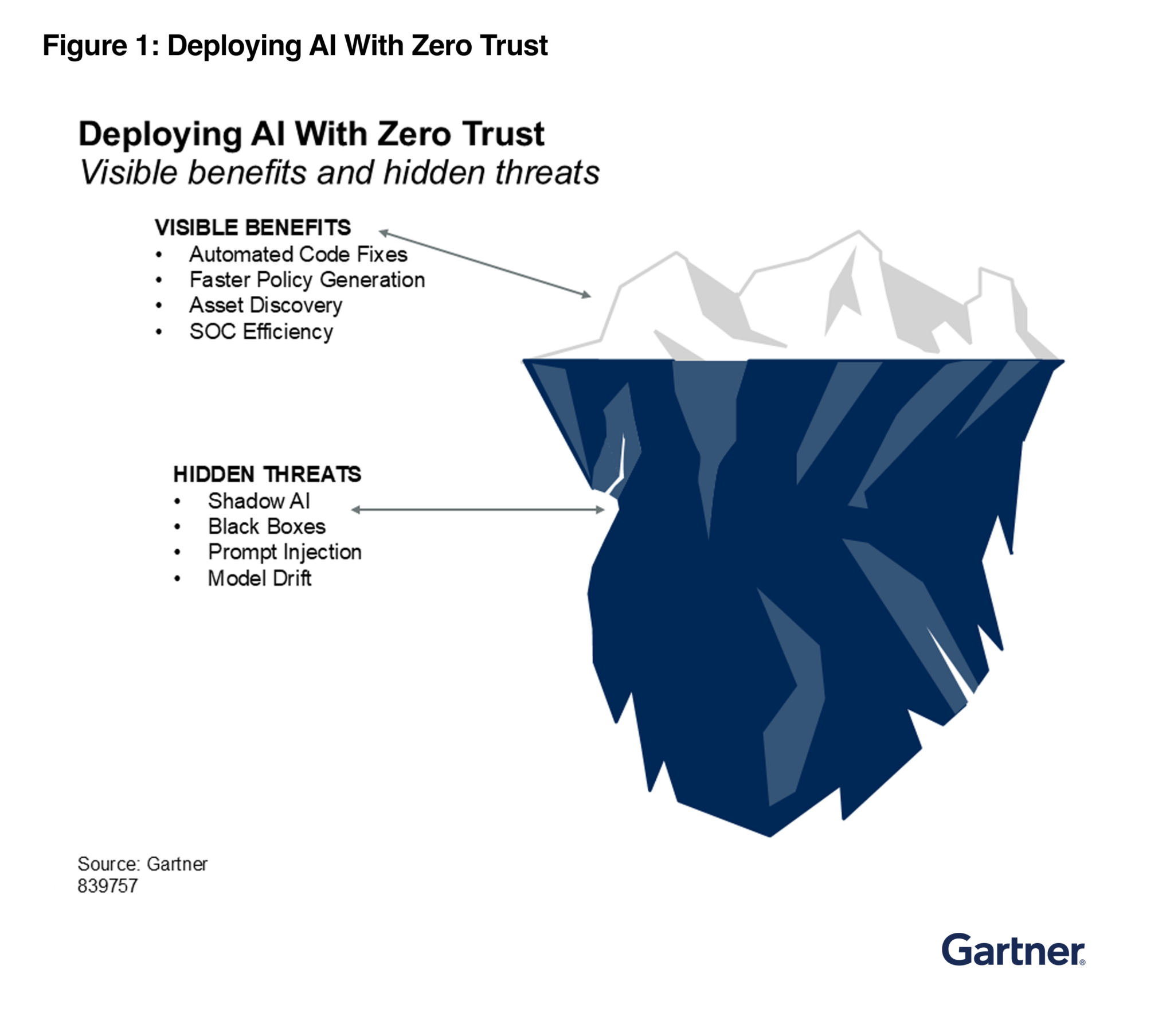
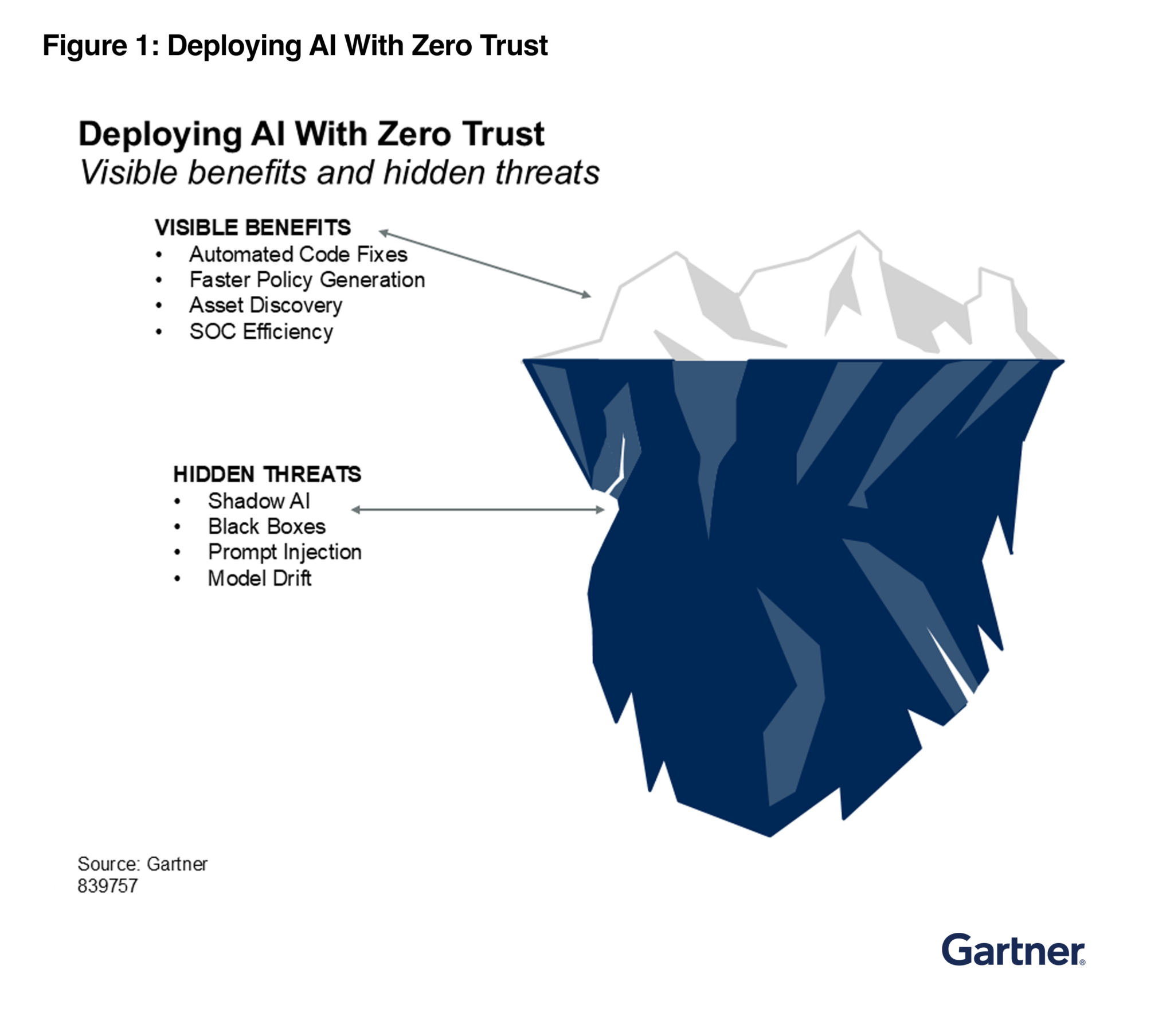
In modern defense and enterprise networks, AI isn’t just a tool, it’s a new identity type with asymmetric risk. Gartner® research reveals that AI can accelerate Zero Trust adoption, but only if you secure the AI first.
Move Beyond Static Security: What You’ll Gain
- Automated Policy: Use AI to turn legacy rules into automated Zero Trust policies.
- Dynamic Trust: Shift from static passwords to real-time, signal-based risk scores.
- Agent Governance: Inventory and control autonomous AI agents with least-privilege.
- Shadow AI Visibility: Locate and block unmanaged AI tools before data leaks.
The Skyhigh Security Advantage: Security at Speed
- Continuous Risk Scoring: Automatically adjust access based on live telemetry.
- AI Discovery: Instant visibility into unmanaged apps and hidden “Shadow” agents.
- Automated Guardrails: Use AI to map and enforce complex policies across your entire cloud.
- Data-Aware Defense: Ensure every entity stays within your Zero Trust boundary.
Disclaimer: Gartner, The AI—Zero-Trust Nexus: How Defense CIOs Secure and Scale AI at Speed, Jay Phipps, Ripley Hunter, Manuel Acosta, George Sellner, 16 April 2026.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Skyhigh Security.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.









