リソース
Resilient Web Access Infrastructure: Business Imperative in a Cloud and Vibe-Code Obsessed World
By Ste Nadin - チーフアーキテクト
April 23, 2026 3 Minute Read

If your online feeds look anything like mine, you’re seeing plenty about what Anthropic can code or the latest AI model a tech influencer built. It’s absolutely cool, but is vibe-coding really top-of-mind for IT & Security leadership? Like my last blog on data protection, this piece focuses on helping practitioners and leaders by spotlighting overlooked security priorities.
For enterprise secure web access, resiliency and productivity often remain the foremost priorities for the C-level staff – CTOs, CIOs, and top-level decision-makers.
Resilient Web Access Infrastructure powered by a Hybrid model is at the foundation of achieving these business priorities and objectives. Secure web access should be about embracing a hybrid approach that unifies the best of all three worlds: web gateways, virtual machines, and cloud.
Innovation Is Moving Fast, but Resilience Isn’t Keeping Up
Modern development cycles reward speed. Teams are incentivized to build, release, and iterate faster than ever before. The consequence? Incredible applications that transform how businesses operate. But there’s a tradeoff happening beneath the surface:
- Infrastructure decisions are being abstracted away
- Security controls are increasingly outsourced to cloud providers
- Resilience is assumed, not engineered
[Developers] → [Cloud Platform] → [Users] = Implicit Trust
This model works—until it doesn’t. When outages occur, or when cloud dependencies fail, organizations quickly realize they’ve built on a single point of failure. As I’m writing this, instability in the Middle East can and has precipitated instability for the cloud.
The Fragility of Cloud-Only Secure Web Access
Secure Web Access is arguably the most critical control point in cybersecurity. It governs how users interact with the internet and filters malicious content. Speaking to our world-class sales reps in the field and at customer sites, vendors offering cloud-only solutions, resilience is directly tied to the availability of their cloud provider.
That introduces a fundamental risk: If the cloud provider experiences downtime → your security stack goes down. If connectivity is disrupted → enforcement becomes inconsistent. If latency spikes → user experience suffers
Cloud-only dependency model in Security Service Edge (SSE):
[User] → [Internet] → [Cloud Secure Web Gateway (Cloud SWG)] → [Policy Enforcement]
Risk Point: Entire web access chain depends on cloud availability
It’s an architectural limitation only fixed by investment. That is investment in a unified web access architecture that offers web gateway deployments in the cloud, on dedicated web gateway appliances, or a range of virtual options (think VMware, Nutanix, OCI!)
Why Hybrid Secure Web Access Matters
A hybrid Secure Web Access approach changes the equation entirely. Instead of relying on a single deployment model, organizations gain flexibility and control by distributing enforcement across three environments:
- On-prem web gateways for data residency and a solid backup from the cloud
- Virtual machines for adaptable, regional deployment
- Cloud enforcement for scalability, global reach, and a very remote workforce
Hybrid model:
User → Traffic Steering Layer:
↘ Cloud SWG
↘ On-Prem Gateway
↘ VM-based SWG
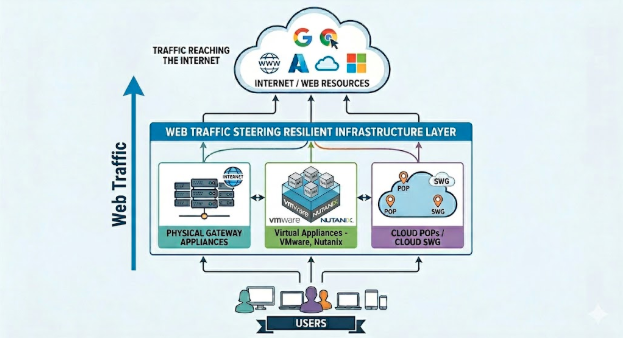
Web access remains steady if the cloud goes down, if appliances fail, or a VM is overloaded.
The Business Case for Resilience
When Secure Web Access fails, the impact goes beyond security gaps:
- Productivity drops as users lose access
- Risk increases as controls are bypassed
- Revenue is impacted during downtime
A hybrid approach ensures continuity. If one layer fails, another seamlessly takes over. That’s the difference between reactive security and engineered resilience.
Skyhigh Security specializes in hybrid deployments. We specialize in providing on prem web gateway appliances that can both keep your data on prem but also give you a backup option if the cloud goes down. We specialize in deploying on a wide range of virtual options, including VMware and OCI. Finally, we specialize in cloud options keeping your security stack modern.
Reach out today to contact a sales team member or see a demo.
著者について

ステ・ナディン
チーフ・アーキテクト
Ste is an Enterprise Architect, performing Chief Architect and CTO roles, with almost 30 years real world experience delivering critical operational systems. Believing in a business outcome first approach he has driven success across a number of highly regulated industry sectors. These have included national critical infrastructure, government, healthcare and security. He is recognized as a leading thinker in the industry performing the roles including that of president for SEMAT.inc working for a common understanding of driving best practice design and delivery.
トレンドブログ
Skyhigh Security Renews IRAP Assessment at PROTECTED Level for 2026
Sarang Warudkar and Stuart Bayliss May 21, 2026
Securing the Fragmentation of the Modern Enterprise: The Data Hosting Conundrum
Ste Nadin May 14, 2026
Skyhigh Security Achieves SOC 2 Type II Compliance for the Complete SSE Cloud Platform
Sarang Warudkar and Stuart Bayliss April 30, 2026
Resilient Web Access Infrastructure: Business Imperative in a Cloud and Vibe-Code Obsessed World
Ste Nadin April 23, 2026











